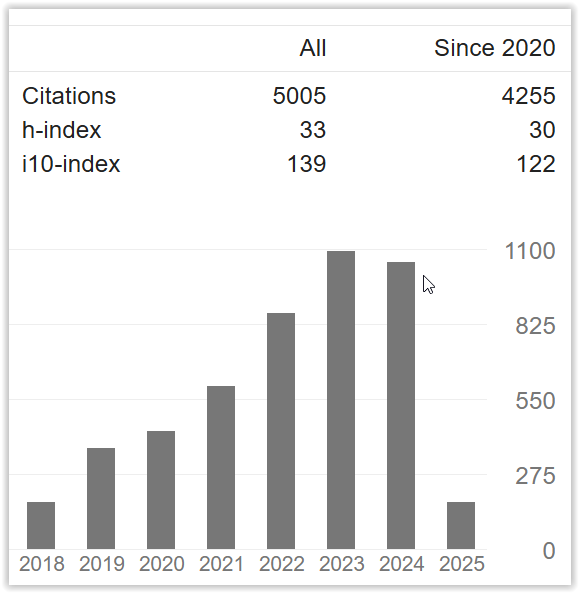
Image Steganography Analysis Using GOST Algorithm and PRNG Based on LSB
DOI:
https://doi.org/10.33633/tc.v21i3.6331Keywords:
GOST, PRNG, Steganography, LSB, ImageAbstract
Security in communication is very important for everyone to pay attention to. To prevent data leakage and illegal retrieval of data, cryptography and steganography can be used. In this study, GOST and XOR LSB with PRNG were used to inject text into images. The final result shows that the combination of these two methods is quite good in terms of image quality, message capacity, embedding speed, and imperceptibility (cannot be seen with the naked eye). Of the 9 image formats tested, 7 images containing messages could be extracted properly with a median MSE of 0.0001935 and a median of PSNR of 85.261. Then, in terms of rotation, all im-age rotations from 90°, 180°, and 270° fail to extract messages and in terms of resizing all sizes from 10%, 30%, 50%, and 80% also fail to extract messages. The average time required for encryption with test data 6 test data is 0.073 seconds with the GOST algorithm, using GOST + XOR LSB with PNRG is 0.485 seconds. By using the XOR combination method LSB with PRNG can store an average of 43.3 bits. From the impercibility test using 5 respondents and visualization using an RGB histogram, it can be seen that there is no difference be-tween the cover image and the stego image.References
I. F. Ashari, “Implementation of Cyber-Physical-Social System Based on Service Oriented Architecture in Smart Tourism Case Study : Bandung Natural Tourism,” J. Appl. Informatics Comput., vol. 4, no. 1, pp. 66–73, 2020.
D. Darwis, “Implementasi Teknik Steganografi Least Significant Bit (LSB) Dan Kompresi Untuk Pengamanan Data Pengiriman Surat Elektronik,” J. Teknoinfo, vol. 10, no. 2, p. 32, 2016, doi: 10.33365/jti.v10i2.8.
B. Nabila and L. T. Sianturi, “Implementasi Fungsi Hash Untuk Mendeteksi Orisinalitas File Audio Menggunakan Metode Gost,” … dan Teknol. Ilm., vol. 8, no. 2, pp. 48–52, 2021, [Online]. Available: http://ejurnal.stmik-budidarma.ac.id/index.php/inti/article/view/2842.
I. F. Ashari, A. J. Aryani, and A. M. Ardhi, “DESIGN AND BUILD INVENTORY MANAGEMENT INFORMATION SYSTEM,” vol. 9, no. 1, pp. 27–35, 2022.
I. F. Ashari, M. Alfarizi, M. N. K, and M. A. H, “Vulnerability Analysis and Proven On The neonime . co Website Using OWASP ZAP 4 and XSpear,” J. Teknol. Komput. dan Sist. Inf., vol. 5, no. 2, pp. 75–81, 2022.
S. G. M. Siregar, “Implementasi Metode Enhanced Audio Steganogafi (EAS) Untuk Penyembunyian Text Terenkripsi Algoritma Gost,” KLIK Kaji. Ilm. Inform. dan Komput., vol. 2, no. 1, pp. 20–27, 2021, [Online]. Available: http://www.djournals.com/klik/article/view/220%0Ahttp://www.djournals.com/klik/article/download/220/158.
I. F. Ashari, “Graph Steganography Based On Multimedia Cover To Improve Security and Capacity,” in 2018 International Conference on Applied Information Technology and Innovation (ICAITI), 2018, no. April 2019, pp. 194–201.
L. Anggriani, “Penerapan Metode Gost Untuk Mendeteksi Keaslian File Dokumen,” TIN Terap. Inform. Nusant., vol. 1, no. 9, pp. 445–450, 2021, [Online]. Available: https://ejurnal.seminar-id.com/index.php/tin/article/view/625.
M. Diana, “Implementasi Metode GOST ( Government Standard ) dan LSB-1 ( Least Significant Bit ) Untuk Mengamankan Teks TIN : Terapan Informatika Nusantara,” Terap. Inform. Nusant., vol. 1, no. 7, pp. 363–382, 2020.
L. P. Malese, “Penyembunyian Pesan Rahasia Pada Citra Digital dengan Teknik Steganografi Menggunakan Metode Least Significant Bit (LSB ),” J. Ilm. Wahana Pendidik. https//jurnal.unibrah.ac.id/index.php/JIWP, vol. 6, no. 3, pp. 295–307, 2020, doi: 10.5281/zenodo.5563416.
N. A. Simatupang and N. A. Hasibuan, “Keamanan File Teks Menggunakan Algoritma Government Standard (GOST),” Pelita Inform. …, vol. 7, pp. 253–257, 2018, [Online]. Available: https://www.ejurnal.stmik-budidarma.ac.id/index.php/pelita/article/view/1091.
J. I. Sari, H. T. Sihotang, and T. Informatika, “Implementasi Penyembunyian Pesan Pada Citra Digital Dengan Menggabungkan Algoritma Hill Cipher Dan Metode Least Significant Bit (LSB),” J. Mantik Penusa, vol. 1, no. 2, pp. 1–8, 2017, [Online]. Available: http://e-jurnal.pelitanusantara.ac.id/index.php/mantik/article/view/253.
I. Dinur, O. Dunkelman, and A. Shamir, “Improved attacks on full GOST,” Lect. Notes Comput. Sci. (including Subser. Lect. Notes Artif. Intell. Lect. Notes Bioinformatics), vol. 7549 LNCS, pp. 9–28, 2012, doi: 10.1007/978-3-642-34047-5_2.
I. F. Ashari, “Aplikasi steganografi pesan teks pada media audio mp3 menggunakan metode penyisipan least significant bit dan advanced encryption standard skripsi,” pp. 1–114, 2015.
A. Riski, H. Purwantoro, and A. Kamsyakawuni, “PENYEMBUNYIAN CIPHERTEXT ALGORITMA GOST PADA CITRA KE DALAM AUDIO DENGAN METODE LEAST SIGNIFICANT BIT Abduh,” J. Ilm. Mat. dan Pendidik. Mat., vol. 10, no. 2, pp. 49–62, 2018.
C. K. Deo, A. Singh, D. K. Singh, and N. K. Soni, “Developing a Highly Secure and High Capacity LSB Steganography Technique using PRNG,” 2020 Int. Conf. Comput. Perform. Eval. ComPE 2020, pp. 136–140, 2020, doi: 10.1109/ComPE49325.2020.9200077.
O. Rachael, S. Misra, R. Ahuja, A. Adewumi, F. Ayeni, and R. Mmaskeliunas, “Image Steganography and Steganalysis Based on Least Significant Bit (LSB),” Lect. Notes Electr. Eng., vol. 605, no. March 2020, pp. 1100–1111, 2020, doi: 10.1007/978-3-030-30577-2_97.
U. Sara, M. Akter, and M. S. Uddin, “Image Quality Assessment through FSIM, SSIM, MSE and PSNR—A Comparative Study,” J. Comput. Commun., vol. 07, no. 03, pp. 8–18, 2019, doi: 10.4236/jcc.2019.73002.
T. Ai Munandar, M. Adelvin L, and A. J. Santoso, “Analisa Psnr, Rasio Kompresi Warna Dan Mse Terhadap Kompresi Image Menggunakan 31 Fungsi Wavelet,” no. October, 2011.
I. Maulana and P. N. Andono, “Analisa Perbandingan Adaptif Median Filter Dan Median Filter Dalam Reduksi Noise Salt & Pepper,” CogITo Smart J., vol. 2, no. 2, p. 157, 2016, doi: 10.31154/cogito.v2i2.26.157-166.
I. F. Ashari, R. Banjarnahor, and D. R. Farida, “Application of Data Mining with the K-Means Clustering Method and Davies Bouldin Index for Grouping IMDB Movies,” vol. 6, no. 1, pp. 7–15, 2022.
T. Limbong et al., “The implementation of computer based instruction model on Gost Algorithm Cryptography Learning,” IOP Conf. Ser. Mater. Sci. Eng., vol. 420, no. 1, 2018, doi: 10.1088/1757-899X/420/1/012094.
G. Hatzivasilis, K. Fysarakis, I. Papaefstathiou, and C. Manifavas, “A review of lightweight block ciphers,” J. Cryptogr. Eng., vol. 8, no. 2, pp. 141–184, 2018, doi: 10.1007/s13389-017-0160-y.
I. F. Ashari and V. Adhelia, “Expert System and IoT for Diagnose of Feline Panleukopenia Virus Using Certainty Factor,” Matrik J. Manajemen, Tek. Inform. dan Rekayasa Komput., vol. 21, no. 2, pp. 451–462, 2022, doi: 10.30812/matrik.v21i2.1517.
I. F. Ashari, M. D. Satria, and M. Idris, “Parking System Optimization Based on IoT using Face and Vehicle Plat Recognition via Amazon Web Service and ESP-32 CAM ( Case Study : Institut Teknologi Sumatera ),” vol. 11, no. 2, pp. 137–153, 2022.
Downloads
Published
Issue
Section
License
Copyright (c) 2022 Ilham Firman Ashari

This work is licensed under a Creative Commons Attribution-NonCommercial 4.0 International License.
License Terms
All articles published in Techno.COM Journal are licensed under the Creative Commons Attribution-NonCommercial 4.0 International (CC BY-NC 4.0). This means:
1. Attribution
Readers and users are free to:
-
Share – Copy and redistribute the material in any medium or format.
-
Adapt – Remix, transform, and build upon the material.
As long as proper credit is given to the original work by citing the author(s) and the journal.
2. Non-Commercial Use
-
The material cannot be used for commercial purposes.
-
Commercial use includes selling the content, using it in commercial advertising, or integrating it into products/services for profit.
3. Rights of Authors
-
Authors retain copyright and grant Techno.COM Journal the right to publish the article.
-
Authors can distribute their work (e.g., in institutional repositories or personal websites) with proper acknowledgment of the journal.
4. No Additional Restrictions
-
The journal cannot apply legal terms or technological measures that restrict others from using the material in ways allowed by the license.
5. Disclaimer
-
The journal is not responsible for how the published content is used by third parties.
-
The opinions expressed in the articles are solely those of the authors.
For more details, visit the Creative Commons License Page:
? https://creativecommons.org/licenses/by-nc/4.0/